TJ's Personal Web Site
At a glance
- Name: TJ Horner
- Work: Site Reliability Engineer at Twosense
- Location: Redmond, WA
- Projects
- Blog
- Résumé
- Hobbies
- 📟 Hardware Design
- 💻 Embedded Development
- 🏠 Home Automation
- 🚴 Cycling
- 🗺 Mapping & Open Data
- Find Me Here
- Fediverse: @tj@tech.lgbt
- Bluesky: @tjtjtj.tj
- GitHub: @tjhorner
- Telegram: @bcrypt
- OpenStreetMap: @tjhorner
- Mapillary: @tjhorner
- Somewhere else? Probably @tjhorner
Selected Projects
Here are some of my recent projects. You can learn about these and more on my GitHub profile.
May 2026
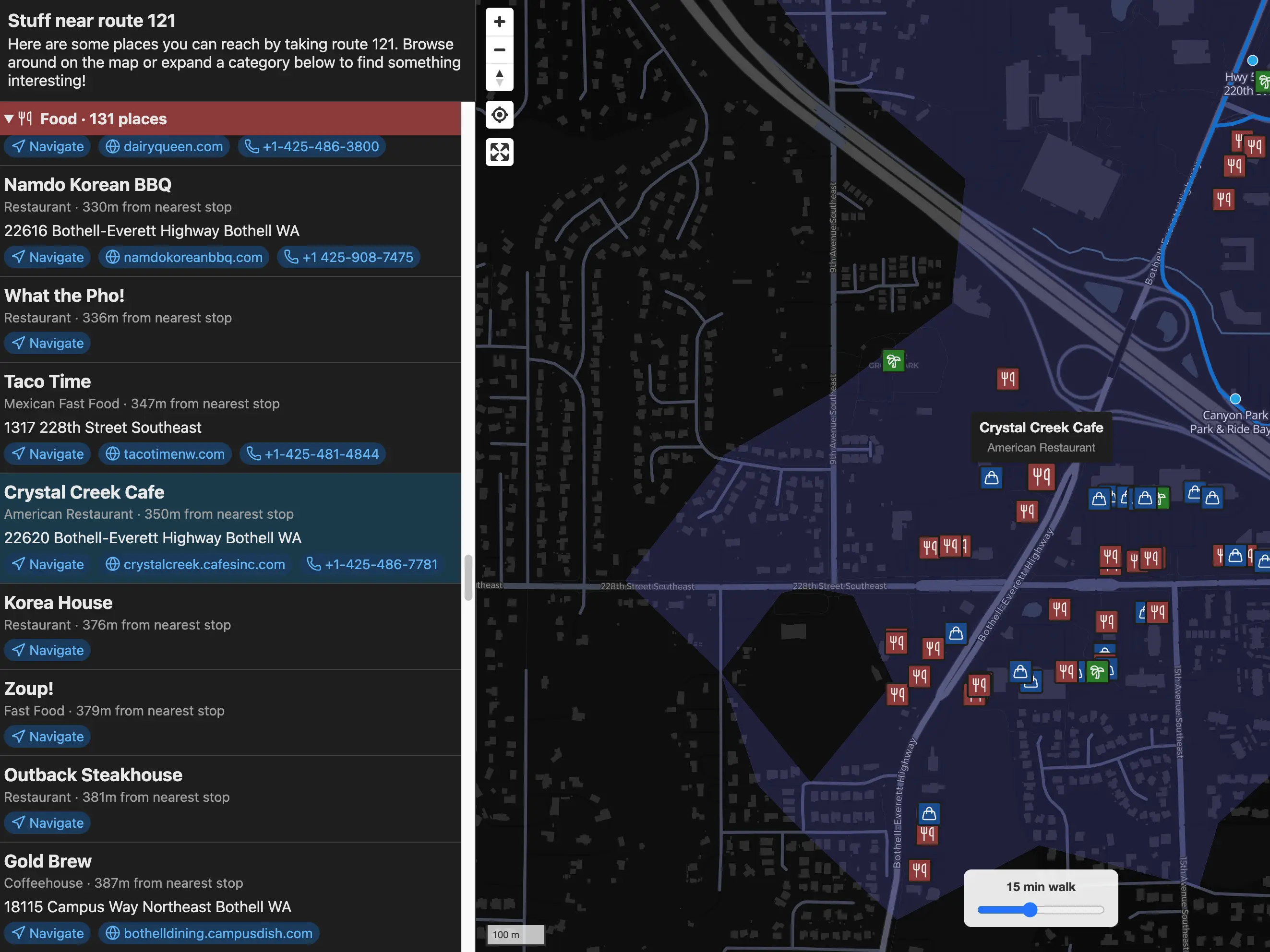
Go By Bus
Discover interesting places accessible from Seattle-area public transit routes
January 2025
Transit Tracker
Open-source DIY public transit arrivals board
September 2024
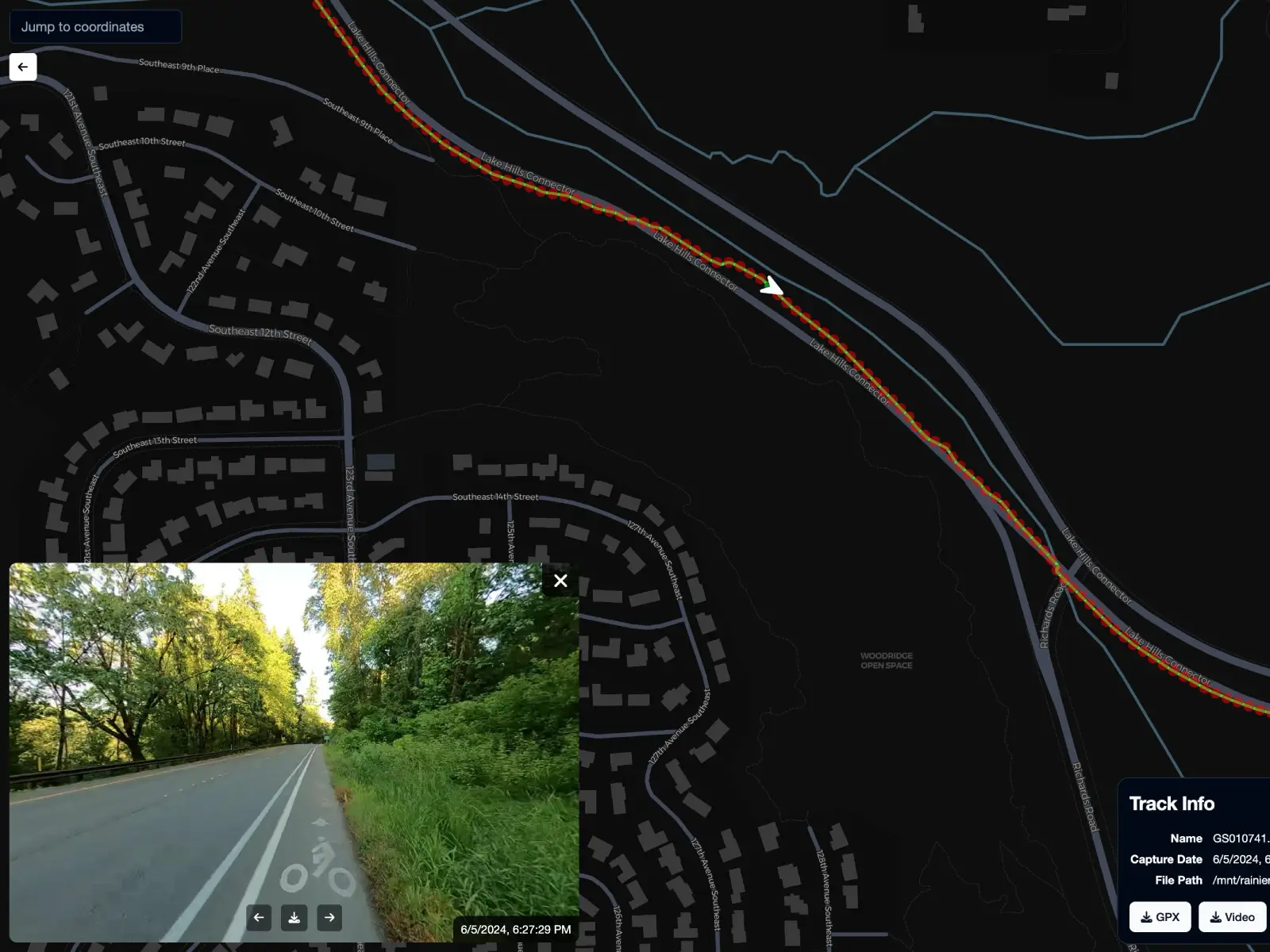
StreetLens
Self-hosted street-level imagery importer and viewer
July 2024
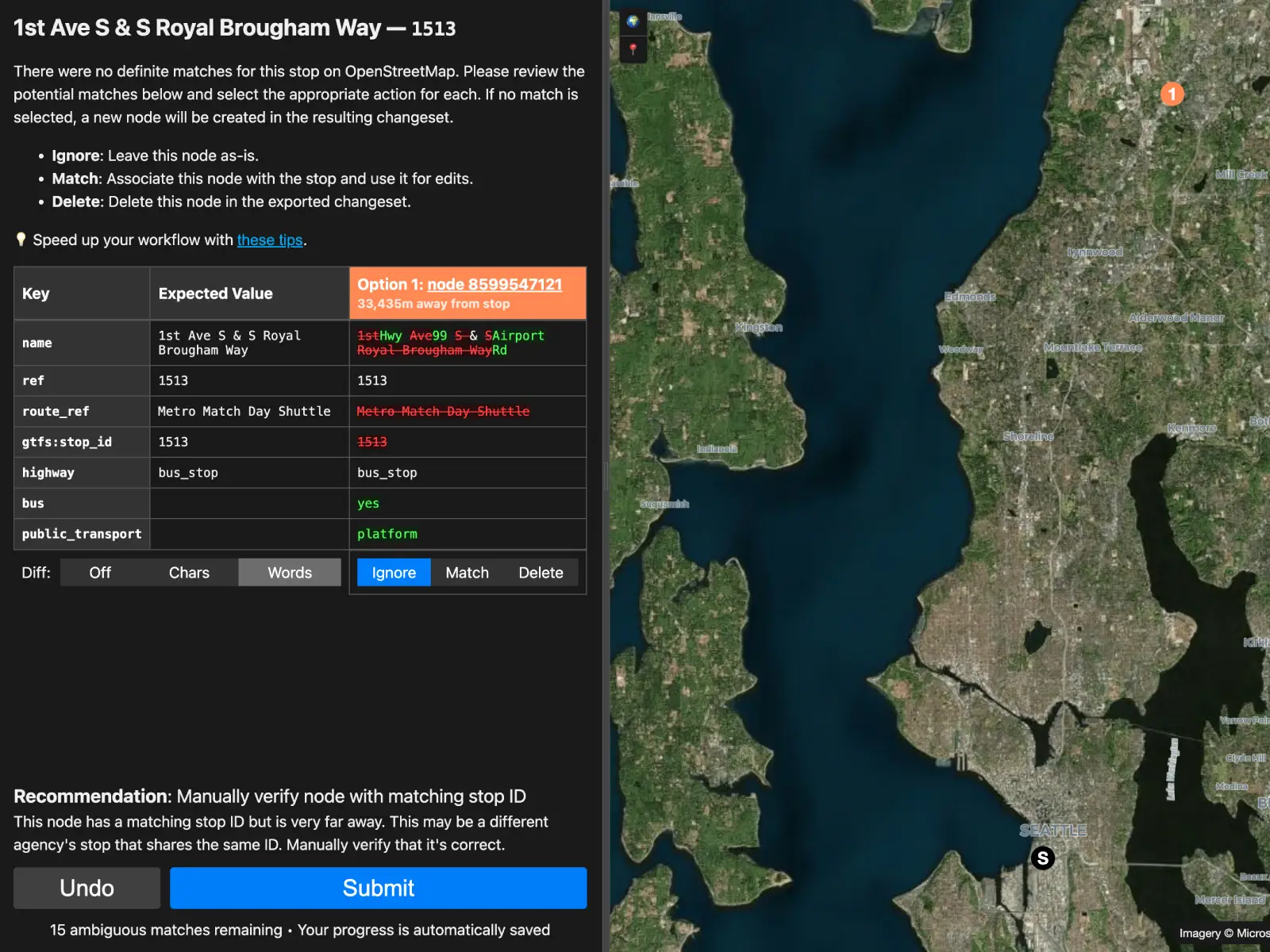
GTFS Janitor
Geospatial conflation engine for maintaining OpenStreetMap with GTFS feeds
July 2024
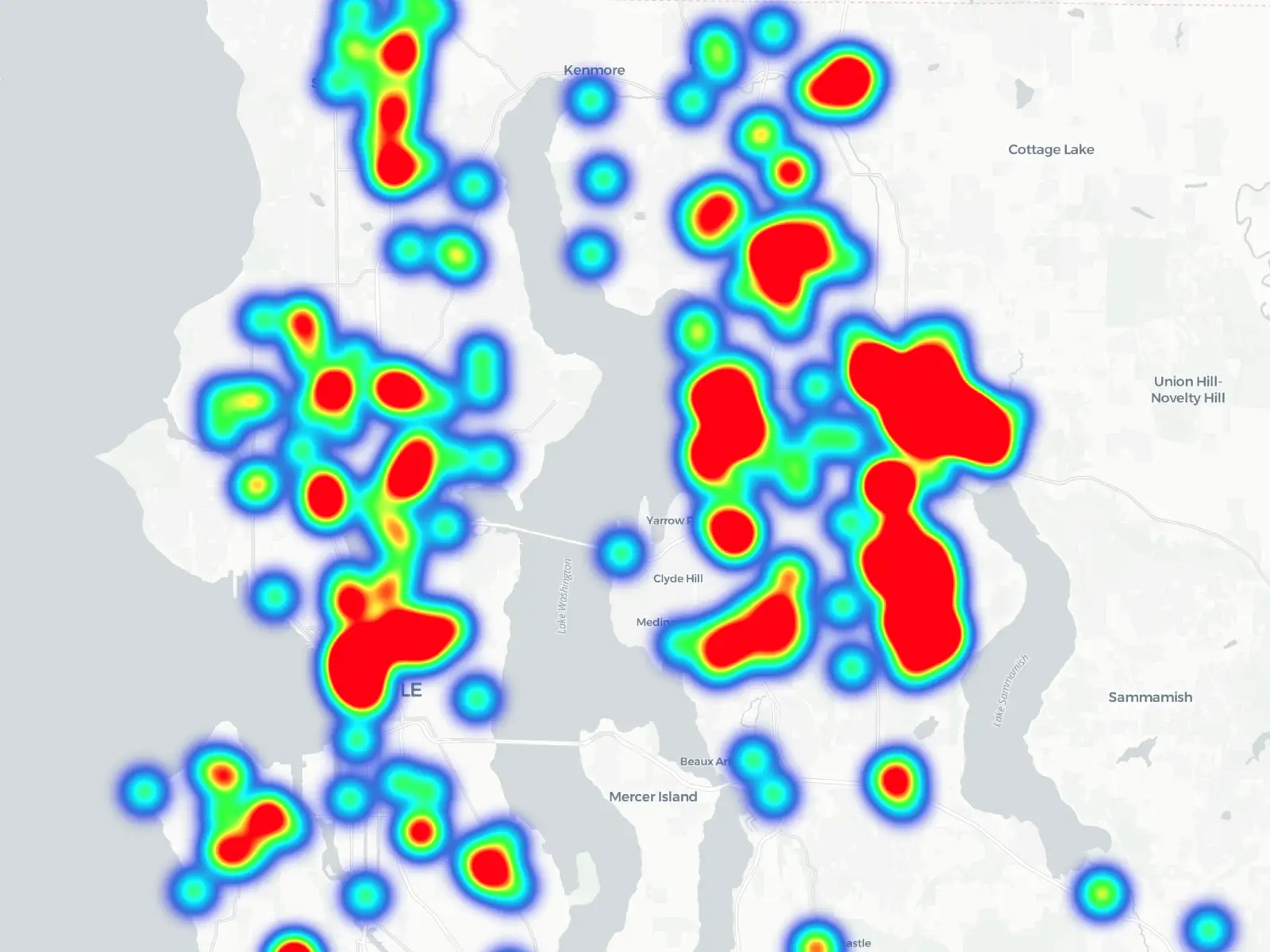
closecall.report
Report near-misses with vehicles on a public crowd-sourced map

August 2022
Upsy Desky
Connect your standing desk to home automation
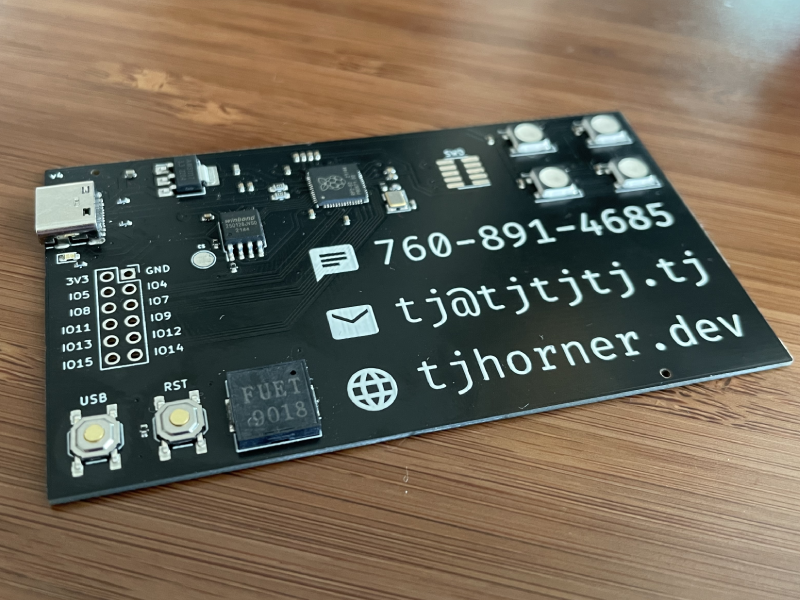
March 2022
PCB Business Card
Functional business card powered by an RP2040
Work
I am a Site Reliability Engineer at Twosense where I work on the platform and backend teams, working with everything from low-level Windows driver APIs to modern web apps.
I previously worked at MakerBot where I made projects that integrated their extensive line of 3D printers with web-based products to better serve their education and professional customers.
More complete work history is available on my résumé.