TJ's Personal Web Site
At a glance
- Name: TJ Horner
- Work: Site Reliability Engineer at Twosense
- Location: Redmond, WA
- Projects
- Blog
- Résumé
- Hobbies
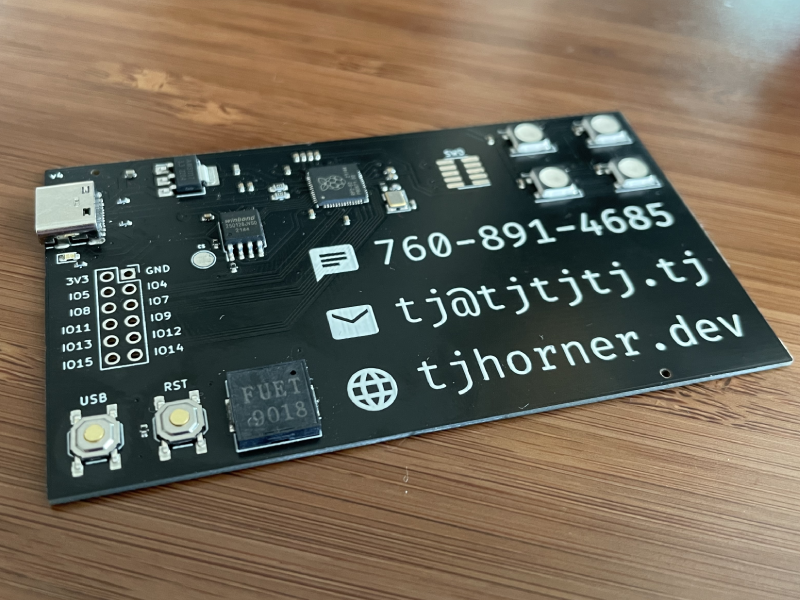
- 📟 Hardware Design
- 💻 Embedded Development
- 🏠 Home Automation
- 🚴 Cycling
- 🗺 Mapping & Open Data
- Find Me Here
- Fediverse: @tj@tech.lgbt
- Bluesky: @tjtjtj.tj
- GitHub: @tjhorner
- Telegram: @bcrypt
- OpenStreetMap: @tjhorner
- Mapillary: @tjhorner
- Somewhere else? Probably @tjhorner
Work
I am a Software Engineer at Twosense where I work on the platform and backend teams, working with everything from low-level Windows driver APIs to modern web apps.
I previously worked at MakerBot where I made projects that integrated their extensive line of 3D printers with web-based products to better serve their education and professional customers.
Selected Projects
Here are some projects I am particularly proud of. You can view these and more on my Notion gallery.